- Human Infrastructure
- Posts
- Human Infrastructure 437: Talk About Your Scripts, Good Advice On AI, Pulling Up Undersea Cables, and More
Human Infrastructure 437: Talk About Your Scripts, Good Advice On AI, Pulling Up Undersea Cables, and More
THIS WEEK’S MUST-READ BLOGS 🤓
This might be one of the most clear-eyed posts I’ve read on AI and AI tools. The author acknowledges the current limits of AI tools (in the context of software development, but they probably apply more broadly): You need to break down a large job into small chunks. You have to provide a lot of context for each chunk. The tools are best when working on well-known problems. And they’ll wander or hallucinate at some point, so you have to pay close attention to their output.
The author also presumes AI tools will get better, faster. Which means technologists shouldn’t ignore them. The trick is to identify two inflection points. What inflection points? “...the one when it becomes relevant to add AI to our portfolio and the other one when the market demands it as our sole approach.”
He writes “...you are not left behind if you do not know perfectly how to use the currently available tools. Actually, most of the knowledge you accumulate today will be worthless in a year or so. Instead, it is important to follow the evolution and understand the technology well enough to know when the inflection points arrive.”
Read the whole post. It’s worth your time. Then think about AI tools and your profession, and consider where and how those inflection points might arise. BTW, this was shared in the Packet Pushers community Slack by Mark Prosser. You can join that community for free, here. - Drew
Consider mentioning your little personal scripts to your co-workers - Chris Siebenmann
https://utcc.utoronto.ca/~cks/space/blog/sysadmin/MentionLittleScripts
Chris suggests that you should tell other people about your collection of weird little scripts probably living in your home directory. If you found a script useful, other people might, too. And that might be the motivation you need to get that script into production-worthy condition. - Ethan
It's not vibe coding: Agentic engineering - Michael Kennedy
https://mkennedy.codes/posts/its-not-vibe-coding-agentic-engineering/
Michael highlights this post drawing a distinction between vibe coding and agentic engineering. In both, AI is used to generate code. But with vibe coding, it’s a YOLO approach. Hurl a prompt at the LLM. If the code that comes back is garbage, then some folks conclude that AI generated code is a waste of time.
So why do many developers find AI a valuable tool? Because they aren’t YOLO’ing a single prompt and expecting a good outcome. Instead, they are creating an entire spec for the software, highly supervising a carefully prompted AI, and pushing the AI generated code through all the testing you’d do on any software project. In this approach, AI isn’t expected to generate perfect code. It’s viewed as a tool that can generate a satisfactory result more quickly than the developer could do without generative AI assistance, even though the AI must be monitored and shepherded through the process. - Ethan
Convergence of Wi-Fi and 5G And the Role Spectrum Plays - Systems Approach
https://systemsapproach.org/2026/02/23/convergence-of-wi-fi-and-5g/
Larry Peterson compares where we’re at with 5G and Wi-Fi as the two technologies continue with their various ecosystems and use case. They share each other’s strategies in many ways—Larry cites OFDMA for example—but the implementations and results tend to be different. 5G is still about guaranteed service, while Wi-Fi is best effort. And will private 5G ever become a widely deployed technology? Larry opines. - Ethan
Don’t Trust Packet Captures on Firewalls - Weberblog
https://weberblog.net/dont-trust-packet-captures-on-firewalls/
Johannes writes about how a built-in packet capture feature on a firewall failed to accurately capture packets. He shows his work to back up his assertion, and concludes with this: “...as soon as you’re dealing with packets that are generated or modified by the firewall itself (routing protocols, NAT, IPsec, TLS interception, etc.), you can’t fully rely on these built-in packet captures.” - Drew
MORE BLOGS
The Challenge of Adding Fiber to Poles - POTs and PANs
Understanding Vlans: A Practical Guide - Ctrl+Alt+Route
The Cook vs. Chef Paradox: Why the Network Engineer Career Ladder Is Breaking - Herve Hildenbrand via LinkedIn

Trying to exit VMware without risk, downtime, or vendor lock-In – but failing?
The challenge is teams treat exits like workload moves, when they're not.
The real challenges are invisible until it's too late: Hidden dependencies that surface during cutover → VMware constructs that don't translate to cloud primitives→ Compliance controls that drift during migration → Manual processes that turn 3-month plans into 18-month nightmares.
FluidCloud, the world’s first and only Cloud Cloning platform, just released a guide on the 5 hardest problems enterprises face when exiting VMware — and what it actually takes to overcome them without disrupting production. Get the guide and learn how companies are achieving true multi-cloud freedom in only 15 minutes, not months – which you don’t have.
→ Get the Guide: https://www.fluidcloud.com/use-cases/escapevmware
→ Learn more about FluidCloud: https://www.fluidcloud.com/
→ Book a demo: https://www.fluidcloud.com/demo
TECH NEWS 📣
Cloud and AWS cost consultant Duckbill expands to software, raises $7.75M for new Skyway platform - GeekWire
https://www.geekwire.com/2026/cloud-and-aws-cost-consultant-duckbill-expands-to-software-raises-7-75m-for-new-skyway-platform/
TL;DR. Corey Quinn & the team at Duckbill Group have been helping companies understand and better control their cloud bills for a long time. Now they’ve raised some money, and they’re building a software platform called Skyway. Duckbill as a service? I expect following Corey on LinkedIn will keep you well informed as to how Skyway is doing, most likely with the cheeky humor Corey’s built his brand on. - Ethan
Say Goodbye to the Undersea Cable That Made the Global Internet Possible - Wired
https://www.wired.com/story/say-goodbye-to-the-undersea-cable-that-made-the-global-internet-possible/
This is a long and winding article about a ship removing the first-ever transatlantic fiber optic cable from the sea floor. The cable went into service in December 1988 and remained in operation until 2002. The article provides a brief history of transatlantic communication (voice, video, and data), and looks at the niche business of removing deprovisioned cables from the ocean. Also, some shark lore. - Drew
New AirSnitch attack breaks Wi-Fi encryption in homes, offices, and enterprises - Ars Technica
https://arstechnica.com/security/2026/02/new-airsnitch-attack-breaks-wi-fi-encryption-in-homes-offices-and-enterprises/
Researchers at UC Riverside and KU Leuven have described techniques to get around cryptographic Wi-Fi protections by bypassing client isolation, which, under certain circumstances, can allow an attacker on a wireless network to act as a man-in-the-middle and intercept traffic meant for other clients. Ars Technica has an overview of the techniques, or you can read the full paper here. - Drew
MORE NEWS
FOR THE LULZ 🤣

Shared by Kaj in the Packet Pushers Community Slack
RESEARCH & RESOURCES 📒
Public Videos: EVPN in MPLS-Based Environments - ipSpace
https://blog.ipspace.net/2026/02/evpn-mpls-videos/
Ivan Pepelnjak continues to make public lots of deep-dive content. The most recent entrants? An EVPN over MPLS video series. - Ethan
Cilium Up and Running is finally available and ready for download - Isovalent Blog
https://isovalent.com/blog/post/cilium-up-and-running/
If Kubernetes networking with Cilium interests you, I suspect this book will be an excellent resource. While it won’t cost you money, it will cost you your contact information. There’s a gate that requires a legit email address to facilitate the download. I tried my normal shenanigans with a phony email address that usually allows me to jump the gate, but was rebuffed. - Ethan
How DNS Works Under the Hood (Packet By Packet) - Chris Greer via YouTube
https://www.youtube.com/watch?v=3FPaTvCJojQ
Chris Greer is putting out a DNS series on YouTube. In this episode, he walks through a Wireshark packet capture of a full DNS recursive lookup to show how a lookup works packet by packet. - Drew
MORE RESOURCES
Talk Python now has a CLI - Talk Python Blog
Like a PBS pledge drive, the time of year has come for the Packet Pushers’ Audience Survey. But instead of calling the station and waiting while Ethan takes down your credit card number, we just need about 10 minutes of your time to let us know what shows you listen to, videos you watch, and a few other questions. It may not seem like much, but this survey really makes a difference.
And if you still want to call Ethan and give him your credit card number, who am I to stop you? Thanks for your support!
INDUSTRY BLOGS & VENDOR ANNOUNCEMENTS 💬
Building for the Big Middle - MaiaEdge Blog
https://maiaedge.io/resources/we-started-maiaedge-to-fix-the-big-middle
MaiaEdge just announced a $20M series A funding round. What does MaiaEdge do? They automate the provisioning of network-to-network interconnects (NNIs) between middle mile providers. MaiaEdge understands the middle mile business and the challenges of NNIs, and are addressing those concerns head on.
In addition to the blog above, read my write up here for more information on what MaiaEdge is doing and how the solution works. If you’ve ever worked with 128T or Acme Packet products, you’ll likely see some similarities. Many of the same folks involved at MaiaEdge. - Ethan
AutoCon 5 Early Bird Registration and Call for Speakers - AutoCon
https://networkautomation.forum/autocon5
The sixth installment of the AutoCon conference, a live event dedicated to advancing the state of the art of network automation, takes place June 8 - 12 in Munich, Germany. Early bird discounts are available for the conference. And if you’ve got something to share about your automation journey in a conference talk, or a workshop you’d like to teach, the Call for Speakers is also open. The Packet Pushers will be there, so go get tickets! - Drew
Cloudflare outage on February 20, 2026 - The Cloudflare Blog
https://blog.cloudflare.com/cloudflare-outage-february-20-2026/
TL;DR. A bunch BYOIP netblocks were withdrawn from the global BGP table by Cloudflare, knocking many customers offline. What happened? Cloudflare was in the process of automating the withdrawal process, but the code incorrectly interpreted an empty string response from their Addressing API as “withdraw all the BYOIP netblock things”. Cloudflare didn’t catch this in testing because their test dataset wasn’t good enough.
Cloudflare is very sorry and reminds you of their Code Orange: Fail Small initiative. They intend to do better and are putting systems in place to put muscle behind that intention. I applaud Cloudflare for their transparency. It’s nice when huge companies tell you what really happened instead of being hand wavy & dismissive. Or outright lying. - Ethan
Is MCP Just Another API Abstraction? - Itential Blog
https://www.itential.com/blog/company/itential-mcp/is-mcp-just-another-api-abstraction/
Itential’s William Collins argues that MCP is not just another API abstraction, but is in fact something else. A layering change. He talks thoughtfully through how he believes MCP is important, underscoring with historical perspective.
If you think MCP isn’t adding anything useful to the network automation mix, give William a chance to change your mind. - Ethan
EmberOT Releases OT PCAP Analyzer v2.0.4 with Major Asset Fidelity Enhancements - EmberOT
https://www.einpresswire.com/article/893106518/emberot-releases-ot-pcap-analyzer-v2-0-4-with-major-asset-fidelity-enhancements
EmberOT has added new features to its OT PCAP analyzer, which is purpose-built to work with protocols and data for industrial control systems. According to the press release, new features include “...improvements to asset fidelity, moving beyond static manufacturer classification to dynamically extract device intelligence directly from observed traffic. Assets identified within uploaded PCAP files can now include hostnames, firmware versions, model numbers, serial numbers, encapsulation context, and object or property identifiers when present in the data.” - Drew
The startup Taalas has an eye-catching idea: to run AI models on custom silicon. Taalas says it can take a brand new model and realize it on custom silicon, optimized for that model, in just two months. Taalas calls this a “Hardcore Model” and claims it can deliver inferencing platforms that “are an order of magnitude faster, cheaper, and lower power than software-based implementations.”
There may be use cases here, though one significant downside is that models advance and improve so rapidly, organizations may not want to tie themselves to purpose-built hardware with a model that might quickly be out of date. - Drew
Running OpenClaw safely: identity, isolation, and runtime risk - Microsoft
https://www.microsoft.com/en-us/security/blog/2026/02/19/running-openclaw-safely-identity-isolation-runtime-risk/
Microsoft probably isn’t the first organization you’d go to for security advice. But in the case of OpenClaw, an open-source AI agent that runs on your local machine and uses your credentials to interact with third-party apps and services to execute tasks, Microsoft may have found an entity more cavalier about security than the Redmond crew.
In this post, Microsoft provides sensible guidance for enterprises experimenting with OpenClaw, and clearly outlines the risks that agents introduce into the environment. It also suggests how to use Microsoft tools and services to minimize the risks from OpenClaw, but there’s good info here whether or not you want to incorporate Microsoft’s products. - Drew
MORE INDUSTRY NOISES
NetBox Labs Announces General Availability of NetBox Copilot, Delivering Enterprise-Ready AI Grounded in Accurate Infrastructure Data - Netbox Labs News
NetBox 4.5.2: Significant Performance Improvements for Scale - NetBox Labs Blog
BlueCat introduces BlueCat Horizon, a SaaS-first Intelligent NetOps platform for cross-domain network operations - BlueCat Press
Cisco Expands AgenticOps Innovations Across Portfolio - Cisco Newsroom
The Mass VMware Exodus That Never Was: The Squeeze Is Just Beginning - Cloudbolt.io
Announcing Support for Service Binding (SVCB and HTTPS) Records - DNSimple Blog
Novel AI Techniques for DNS Tunnel Security - Infoblox Security Blog
VPP SRv6 L2VPN - IPng Networks
When “Nearby” Isn’t Nearby: How Remote Peering Undermines Anycast - Internet Society Pulse
DYSTOPIA IRL 🐙
TOO MANY LINKS WOULD NEVER BE ENOUGH 🐳
LAST LAUGH 😆
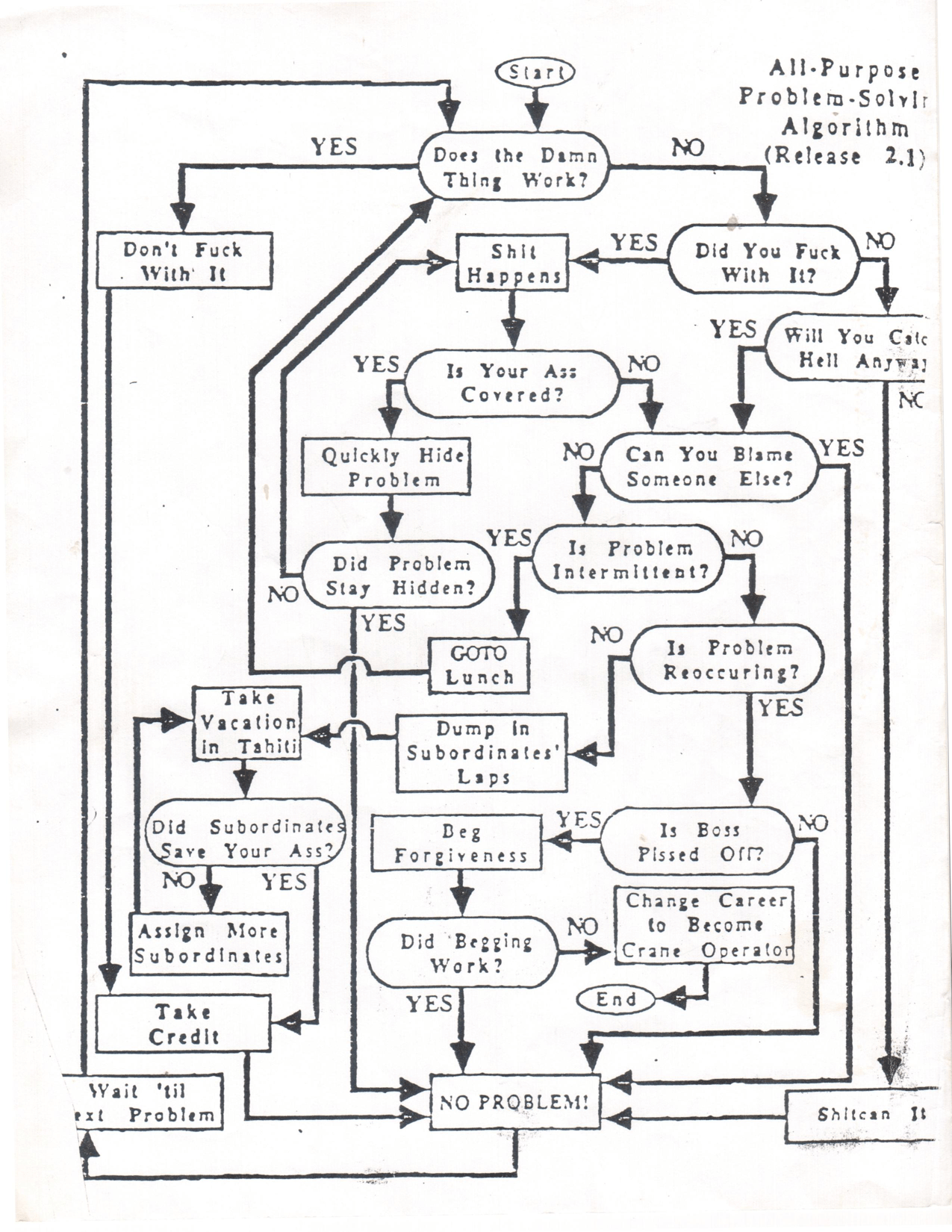
Bell Labs Universal Troubleshooting Flow Chart
Shared by Steve P. on the Packet Pushers Community Slack. Steve got it from his father, a Bell Labs tech.

